Idea 1
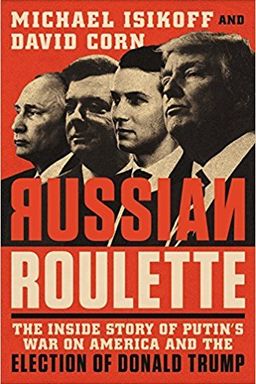
Russia, Power, and the 2016 Political Web
You can think of this book as an anatomy of modern influence—how Russian power strategies evolved from Cold War espionage into cyber age manipulation and how those tactics intersected with Donald Trump’s business life and the 2016 election. Across its chapters, you watch personal ambition, digital deception, and geopolitical rivalry merge into one narrative of hybrid conflict and political vulnerability.
From Business Ties to Political Exposure
The first thread follows Trump’s long pursuit of deals in Russia: his partnership efforts with Aras and Emin Agalarov after Miss Universe 2013, subsequent negotiations through Felix Sater for Trump Tower Moscow, and multiple attempts to gain Kremlin signoff on real estate branding. These decades of overtures formed a business-political nexus that blurred lines between private aspiration and national interest—an important source of scrutiny as Trump later ran for president.
(Note: Similar patterns of personal diplomacy shaping foreign exposure appeared in books about oligarchic networks by Catherine Belton and Masha Gessen.)
Geopolitical Turn: From Reset to Rivalry
In parallel, the U.S.–Russia relationship transformed during the Obama years. Efforts at an early-term "reset" collapsed after Russia’s invasion of Ukraine and the Magnitsky Act’s sanctions. These events set the stage for Russia’s antagonism toward Western institutions and pushed the Kremlin toward active measures—covert methods blending intelligence, hacking, and propaganda aimed at weakening opponents without traditional military confrontation.
Kompromat and Covert Leverage
The book situates kompromat, or compromising material, as a longstanding Russian tactic—stretching from the Yury Skuratov scandal of 1999 to the Litvinenko poisoning in 2006 and into modern cyber-enabled leaks. Putin’s inner circle learned that personal or political exposure can yield control; kompromat thus became both deterrent and weapon. By the time the 2016 race unfolded, email hacks and timed leaks functioned as digital kompromat—reshaping perception rather than coercing directly.
Digital Hybrid Warfare
General Valery Gerasimov’s 2013 doctrine reframed war as a continuum of informational, economic, and psychological pressure. You see how this played out through troll farms like the Internet Research Agency (IRA), cyber intrusions by groups known as Cozy Bear and Fancy Bear, and the coordinated use of state outlets RT and Sputnik. Together, they ran not only theft operations (as in the DNC hack) but intentional release campaigns designed to polarize voters and undermine faith in democratic systems.
Campaign Contacts and Counterintelligence
These digital tactics met fertile ground in an American campaign eager for foreign-sourced opposition research. You follow figures like George Papadopoulos hearing rumors of Russian "dirt" on Hillary Clinton, Trump Jr.’s willingness to meet Natalia Veselnitskaya, and Paul Manafort’s emails to Oleg Deripaska’s aide. Those interactions motivated FBI counterintelligence action—beginning with Papadopoulos’s tip and expanding into secret FISA surveillance on Carter Page.
Information Warfare in Practice
The DNC and Podesta email releases showcased the full orchestration: intelligence theft paired with timed disclosure through WikiLeaks to dominate the news cycle. Social-media manipulation amplified fallout as the IRA’s U.S.-targeted personas spread divisive ads and memes. Media coverage reacted mostly to content, not attribution, which is precisely what Russian strategists intended—to redirect focus from "who did this" to "what was said."
Government Deliberations and Policy Constraint
Inside Washington, national-security principals debated action. Susan Rice, John Brennan, and James Clapper weighed sanctions, disclosure, and cyber retaliation. Their caution reflected fear of escalation and politicization. Ultimately, the October 7, 2016, ODNI/DHS statement publicly attributed the operation to senior Russian officials—but the announcement was overshadowed the same day by the explosive Access Hollywood tape, demonstrating how media timing neutralized state-level messaging.
Transition and Consequences
After the election, Obama’s administration expelled diplomats and imposed sanctions. However, Trump transition contacts—Michael Flynn’s calls with Russian Ambassador Kislyak and Jared Kushner’s meeting with banker Sergey Gorkov—raised new alarms. These episodes laid groundwork for congressional and special-counsel investigations that defined U.S. politics in 2017 and beyond.
Central takeaway
Across all parts, you witness the collision of personal ambition, systemic vulnerability, and foreign exploitation. Russia’s updated hybrid warfare meets an American political culture unhardened against informational attack—producing a case study in how state power can weaponize openness, media, and ego to achieve strategic disruption.
This synthesis invites you to connect cues: real estate overtures preluding political flirtations; cyber intrusions morphing into public leaks; cautious policymaking setting conditions for misinformation; and an enduring lesson—that transparency itself can be turned into a tool for control when adversaries master its rhythms better than democracies do.