Idea 1
Curiosity, Systems, and the Making of a Hacker
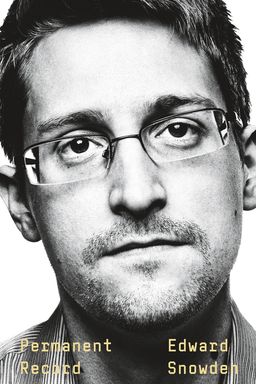
How does a child’s curiosity evolve into a global act of whistleblowing? In Permanent Record, Edward Snowden charts his transformation from an inquisitive boy fascinated by machines into a systems thinker who exposes one of the largest surveillance expansions in history. You follow the arc from early tinkering through technical immersion, institutional loyalty, discovery of wrongdoing, and finally the moral decision to disclose. The book is less about one man's rebellion and more about how everyday curiosity can illuminate—and threaten—the architecture of power.
Origins of Agency and Systems Thinking
Snowden's formative experiences with household technology, especially the Commodore 64, teach him cause and effect through play. By rolling back the kitchen clock to stay up late, he learns early that systems can be manipulated if you understand their controls. The NES repair sessions with his father Lon further reinforce a philosophy of repair over replacement: understanding failure is part of mastery. These small acts of curiosity create the foundation for the moral and technical consciousness that drives his later life in intelligence.
Identity and the Internet
Fast-forward to the 1990s Internet, where pseudonyms and chat rooms let adolescents reinvent themselves endlessly. Snowden’s handles—like “sq33ker” and “Belgarion”—show you how online anonymity enabled authentic exploration without fear of permanent consequence. This was the prototype of a world before social media’s real-name permanence. The generosity of early online communities, where experts freely mentored the curious, shaped his sense of collaborative learning and fluid identity—the very opposite of the surveillance culture he would later resist.
Institutions, Records, and Authority
Snowden’s schooling and family life introduce the theme of surveillance and accountability in miniature. The threat of a “permanent record” in school becomes a haunting metaphor once he enters government systems that truly record everything. His parents’ divorce teaches compartmentalization—the skill of managing truths across contexts. Later, when applying for clearance, he chooses not to scrub his digital history, accepting the idea that real integrity means living transparently with your past rather than rewriting it.
From Curiosity to Conscience
Each stage builds a pattern: curiosity leads to control, control reveals system failures, and revelation triggers moral questioning. His early hack at Los Alamos, where he responsibly reports a vulnerability instead of exploiting it, offers a miniature rehearsal for his later global disclosure. For Snowden, hacking becomes an ethical inquiry—how systems can be improved rather than abused. That ethic persists even when institutional loyalties demand silence.
Technology and Power
Inside the CIA and NSA, Snowden encounters the scale of technological systems that record human life. These environments, rich in ritual and secrecy, teach him how agency and authority are encoded in software. EPICSHELTER, STELLARWIND, and PRISM aren’t mere programs; they are the materialization of an idea—that safety can justify omniscience. As Snowden uncovers how words like “acquire” are redefined to legalize mass data retention, he realizes the same systems curiosity that made him an effective technician also gives him unique visibility into ethical rot.
Key pattern: Observation becomes obligation
By knowing systems deeply, Snowden cannot remain a passive witness. The book shows how understanding confers responsibility: once you see how the machinery of surveillance consumes privacy, the choice to act becomes moral necessity.
Overall, Permanent Record suggests that curiosity, technical fluency, and moral courage are interconnected. The act of learning how things work—whether clocks, code, or countries—can lead you to question who decides they should work that way. Snowden’s story asks whether knowledge without accountability is freedom or merely another form of control—and dares you to consider your own role within the systems you inhabit.