Idea 1
Secrecy, Power, and Democratic Drift
Secrecy, Power, and Democratic Drift
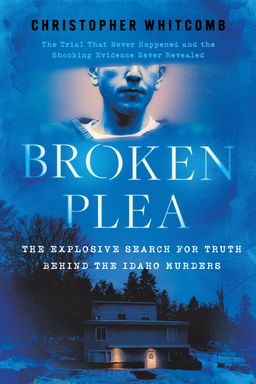
How do you protect a nation without losing it? Broken Plea argues that the most dangerous threats emerge where covert power, corporate technology, and political urgency converge. The novel contends that secrecy expands during crises—hybrid terror at home and abroad—while legal guardrails bend, corporate actors step into state functions, and leaders make high-velocity trade-offs that can quietly realign the constitutional order.
The triangle: covert action, corporations, and the presidency
You watch a tight triangle harden: covert operators (FBI HRT, CIA case officers, JSOC units), corporate intelligence (Borders Atlantic, Quantis), and the executive (President David Ray Venable, Vice President Elizabeth Beechum). The Indonesian raid to seize Ali Fallal Mahar is the template. Jeremy Waller and a multinational task force execute kinetic mastery while the White House and a private CEO, Jordan Mitchell, monitor live satellite feeds. When GI Jane kills Mahar on-site—and even mutilates prisoners for biometric trophies—the act travels instantly from field to boardroom to Oval Office, becoming political currency more than accountable evidence.
In that transmission chain, oversight thins. The boardroom mantra—"This is a one-time opportunity"—captures how urgency rationalizes bypassing law. The planning cell expects no after-action hearings; the vice president sees black programs as tools, not exceptions. You realize why the novel keeps showing you executives in shadow operations: when public fear spikes, nontransparent machinery swells to fill the vacuum.
Hybrid terror as the accelerant
Crisis fuels the drift. Simultaneous IEDs in Atlanta, Anaheim, and Bloomington detonate within eight seconds. Snipers with Barrett .50-cal rifles threaten airliners. Finance, encrypted comms (Quantis phones), and cyber probes merge with bombs and guns. The shock isn’t only the casualties; it’s the system strain. You feel the book’s systems-theory warning: attackers succeed by syncing vectors across physical, financial, and digital domains, while defenders default to silos. The larger the operational canvas, the more tempting it becomes for leaders to reach into the black toolkit—quickly, quietly, expansively.
The crypto hinge: Quantis and the keyholder problem
Quantis sits at the pivot. Mitchell’s firm claims a practical leap (the Nguyen cornerstone that collapses hard math into deployable crypto), placing the company at the center of state secrecy and criminal concealment. Its secret‑sharing architecture relies on a handful of trusted principals. That social design—trust compressed into few hands—creates single points of catastrophic failure. When Ravi and Sirad trace an insider breach through anomalous timestamps to a WHCA dog‑ear called CAPSTONE3, you see the nightmare: if you inhabit the trust anchors (WHCA, DSNET3), you can shape presidential communications, even nuclear authentication pathways. Power in the novel is whoever holds the keys—or can mimic the keyholders.
Law under pressure: from norms to necessity
The war on terror corrodes legal lines. Renditions become routine; FBI/HRT morphs from law enforcer to co‑belligerent. GI Jane’s Guantánamo interrogations, the treatment of Ashar al Bayad, and covert killings blur the boundary between security and brutality. Then the presidency itself frays: a sleep-deprived Venable hallucinates while Beechum quietly orders sedation rather than immediately invoke the Twenty-Fifth. The book’s argument is not that law vanishes; it’s that law bends first in the shadows—where time pressure, media panic, and plausible deniability coexist.
False flags and domestic mirrors
The most chilling engine of drift is misattribution. Colonel Buck Ellis’s Phineas Priesthood stages Islamist signatures—audio claims by "Ansar ins Allah," Arabic cues—to mask a domestic plot, Megiddo. RDDs at Cal‑ISO in Folsom and infrastructure hits aim to trigger U.S. retaliation against Saudi targets, manufacturing a civilizational clash. The twist that American extremists trained at the Homestead overlap with foreigners (three Americans in Mahar’s camp) forces you to abandon clean threat boxes. When attribution wobbles, narrative entrepreneurs—politicians and CEOs alike—can steer policy toward their preferred enemies.
Key Idea
Secrecy expands fastest where fear, technology, and plausible deniability meet—and it rarely contracts without deliberate accountability.
The human stakes
The argument would feel abstract if not for the Waller family. Jeremy’s deep-cover work at the Homestead collides with Ellis’s abduction of Caroline and their children. Jeremy’s desperate traffic crash gambit to summon police, Christopher’s broken arm, and Maddy’s bruises strip away policy distance. The novel insists: institutional choices echo in kitchens and cellars. Victory measured only by plots foiled ignores the debris left in marriages, childhoods, and operator psyches.
What you carry forward
You finish with a framework. Think in systems: hybrid threats, keyholder vulnerabilities, and narrative manipulation. Watch for democratic drift: executive shortcuts, corporate custodianship of secrets, and false‑flag optics. And count the human cost as part of operational calculus, not its aftermath. (Note: Readers of le Carré or William Gibson will recognize the blend of moral ambiguity and techno-politics; Broken Plea adds the domestic extremism twist.) The book’s quiet thesis is stark: if you don’t police the intersection of secrecy and power, you may win the battle and misplace the republic.